Learn here how to configure Azure Files with Active Directory (AD) authentication for Azure Virtual Desktop – FSLogix Profile Container and MSIX app attach
Good news, more PaaS for DaaS! While we are all participants in the digital transformation, leveraging platform (PaaS) services is always something to first take into consideration over Infrastructure Services (IaaS). Azure File is a platform service as part of your Azure storage account and is now supported for ADDS in public preview.
“Our industry does not respect tradition. What it respects is innovation.” ― Satya Nadella
In traditional virtual desktop infrastructure (VDI) deployments scenarios, it was/is still most likely that you build your own SMB file infrastructure to storage your roaming profiles and user-specific data on. This creates extra management and maintenance overhead, increases costs, and requires physical hardware expansions during upgrade to burst (CapEx) – non-flexible.
The Azure files (Storage-as-a) service on Azure is scalable on-demand, you just create your storage account, create a file share, setup the designated NTFS/ACLs and you are ready to use it – all based on the OpEx billing model. If you want more storage? Just expand the quota and you have more. Your billing model adjusts automatically. How this works in conjunction with Azure Virtual Desktop with FSLogix Profile Container and MSIX app attach is something you’ll learn in this article. Happy learning/reading!
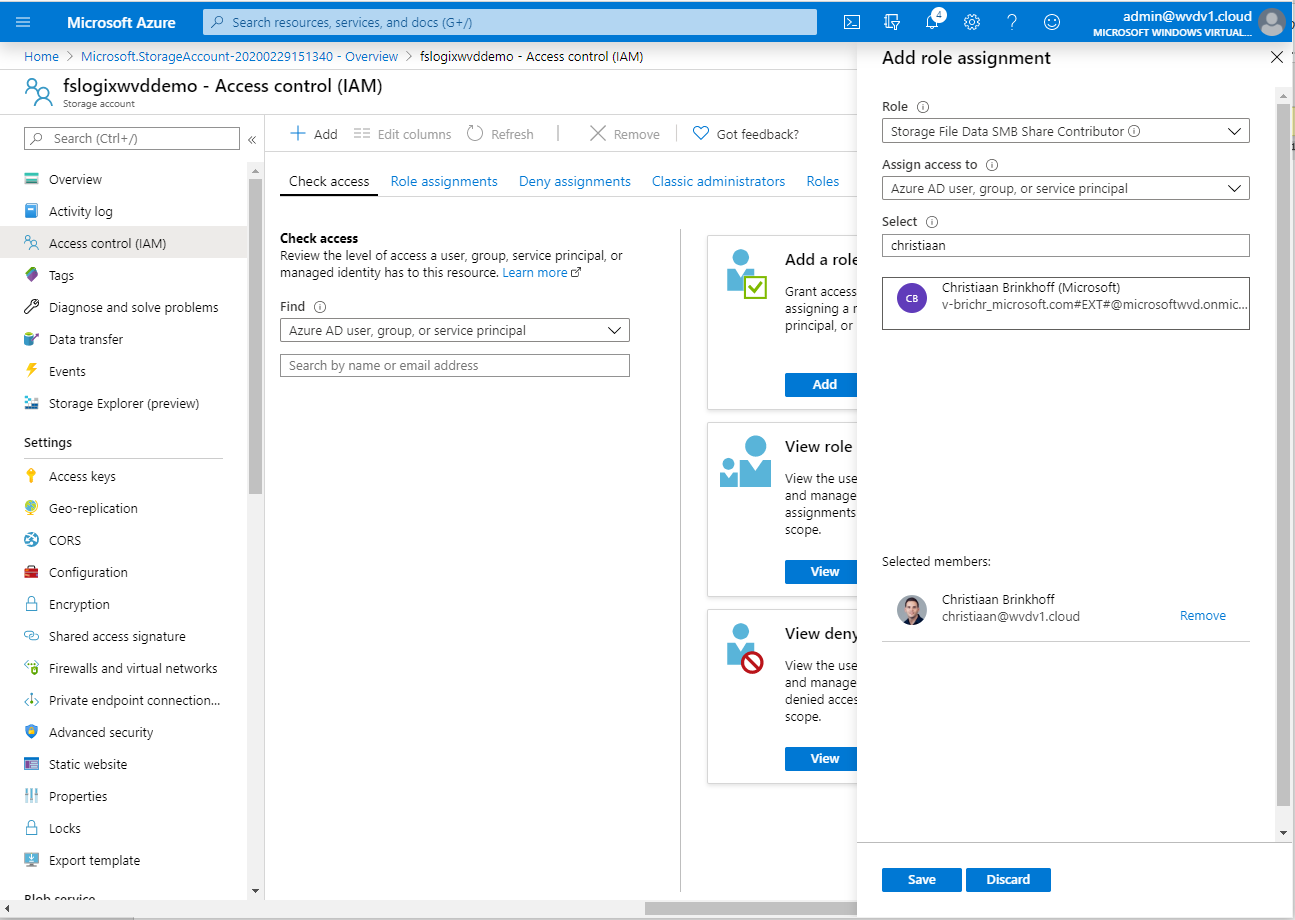
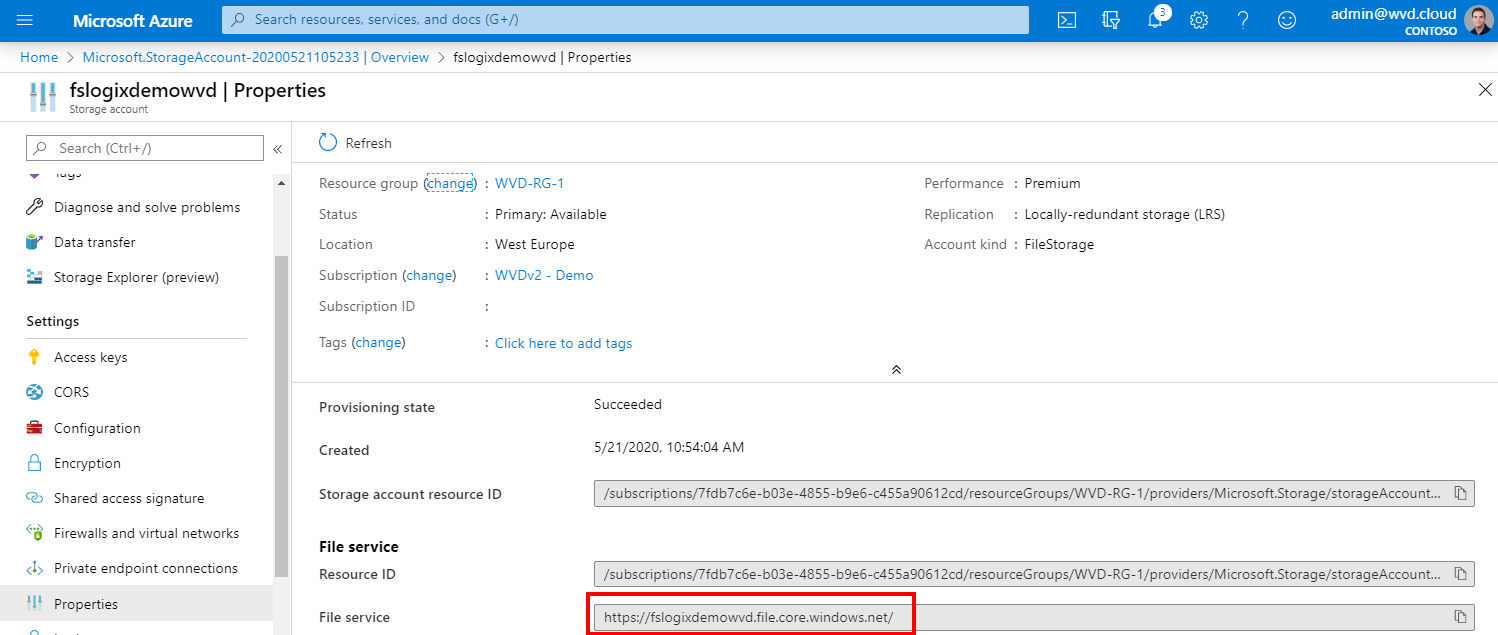
When you’re done with this article – the following section should show up at the properties of your storage account.
Table of Contents
Click on the title to jump to that spot in this article:
- Migrate to FSLogix Profile Container
- Private endpoints
- Pre-requirements for Azure Files
- How to configure Azure Files for Active Directory (AD)
- Load Azure Hybrid Storage modules
- Activate Azure Files – AD authentication on your storage account
- Configure Azure IAM permissions
- Verify your Azure Files SMB Share
- Using it for MSIX app attach?
- Configure NTFS rights on the Azure Files Share
- FSLogix Profile Container configuration
- Scale your Azure Files environment
- MSIX app attach Rights NTFS/IAM RBAC configuration
- Verify the configuration
- End-user – experience video
Migrate to FSLogix Profile Container
To provide a good migration path between your existing profile delivery/management solution to FSLogix Profile Container, the AVD Engineering team has created a migration script that is currently available as a Private Preview. The migration script will allow you to perform mass conversions of user-profiles from various (specified) types to FSLogix based Profile Containers at scale.
Note: You can use the migration script for Roaming Profiles, UPD and UPM. Read more about it here in one of my other blogs.
Once you have the migration script, follow the steps below.
- Place the FSLogixMigration Folder in a module directory,
- import the module with the command – Import-Module FSLogixMigration
- If the module is imported successfully you will see the welcome message.
- At the time of import, a check will be done for the following modules: ActiveDirectory, Hyper-V, Pester
Private Endpoints
You can use private endpoints for your Azure Files – Storage accounts. Private Endpoints allow clients on a virtual network (VNet) to secure access data over a Private Link. The private endpoint connection connects over your VNET to the backbone of Azure to the Storage account – without going over the internet. This could be beneficial from an performance and security perspective. Learn here how to configure the private endpoint via the Azure Portal on Microsoft Docs here.
Azure Files with AD – pre-requirements
- Traditional AD environment synchronized to Azure AD with Azure AD Connect
- Azure Virtual Desktops VMs need to be active in Active Directory
- Account credentials to perform the steps below to create a computer account in an existing Active Directory environment to connect with Azure Files.
- Make sure to deploy your storage account in one of the supported Azure regions.
- Use Premium Performance for larger-scale environments.
- Azure administrator/contributor / delegated rights to create the storage account
How to configure Azure Files for Active Directory (ADDS)
When you haven’t done this yet. Please create a storage account within your Azure subscription.
Enter your Azure subscription specific details and a lower-cased name for the storage account group.
FileStorage or StorageV2 as account type can be selected for Azure Files depending on your Azure datacenter location and if you go for Standard or Premium.
Select Premium storage when you need more IOPs capacity. More info here.
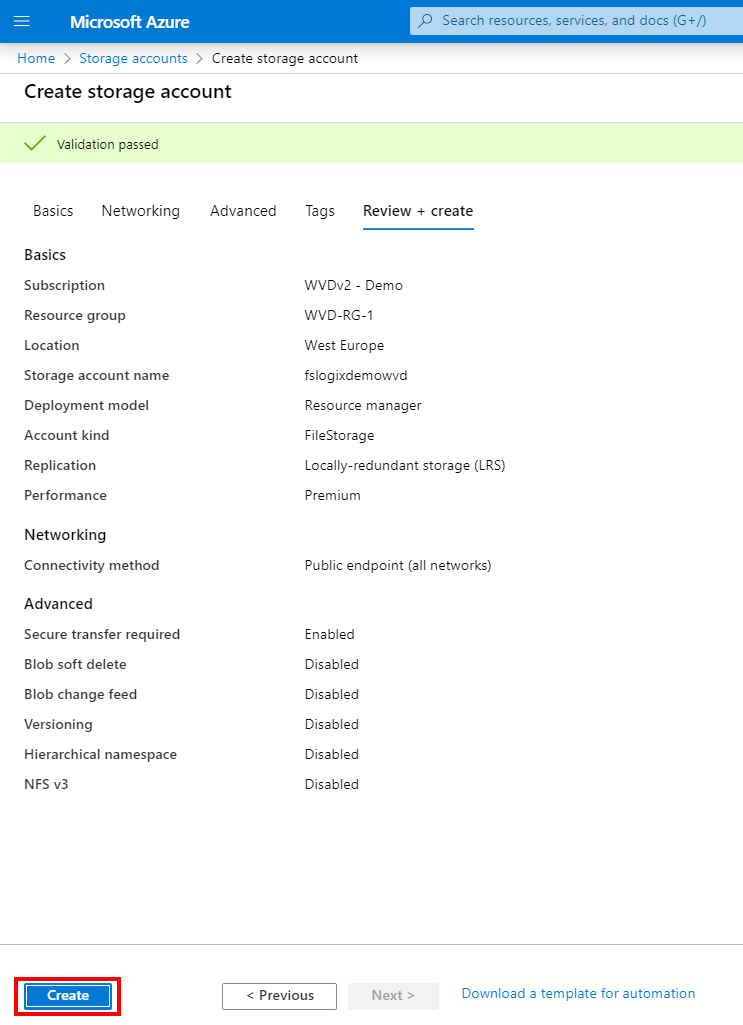
Click on Review + Create
Note: Make sure to create a unique storage account name no longer than 15 characters. Kerberos has a hard limit of a maximum of 15 characters. The Azure Storage Hybrid module to make AD authentication work automatically creates a computer account based on your storage account name in your activate directory environment to provide the authentication. When the storage account name is longer than 15 characters – the process will fail in the creation of the computer account.
Note: The preview is currently available in Azure West Europe and almost every Azure datacenter region. See here what locations aren’t supported yet. They will be added soon.
Click on Create
Finished successfully…
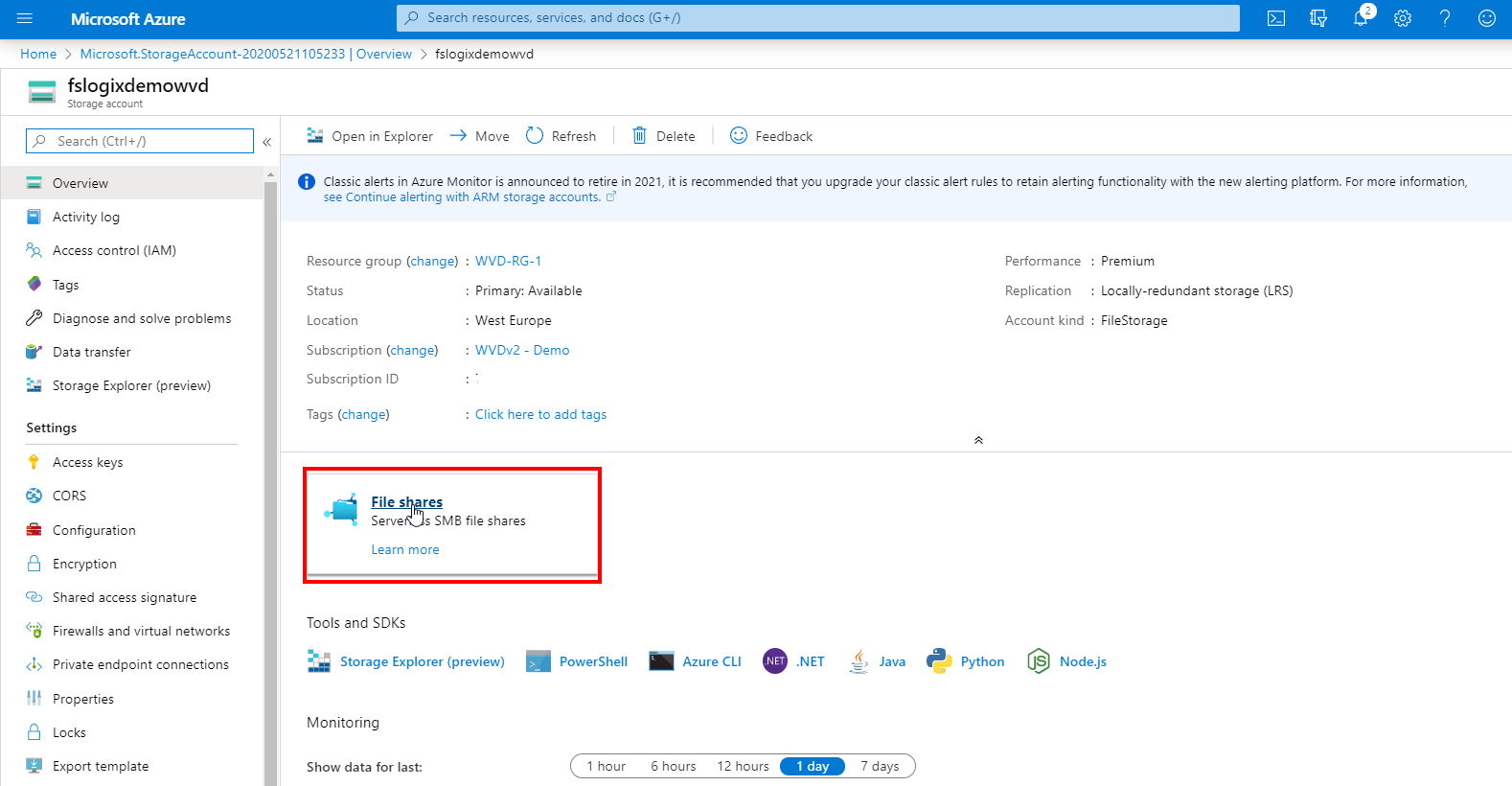
Open the new storage account / Go to the resource
Go to File shares
Create the FSLogix Profiles share
Note: When choosing Premium Files, make sure to (pre)provision the capacity that accommodates the level of IOPs for the users that are logging on. 1GB = 1 IOP with a bursting capacity x3 for 60 minutes. Read more about it here.
Create the MSIX app attach share (optional)
Activate Azure Files – Active Directory authentication on your storage account
Download and unzip the AzFilesHybrid PowerShell module. Make sure to download the latest version.
Store the data somewhere you prefer e.g. C:\AzFilesHybrid.
Note: Make sure you import the AZ module, which is needed to perform the steps below.
Install-Module AZ
Import-Module AZ
Note: Are you getting this error: WARNING: Unable to download from URI ‘https://go.microsoft.com/fwlink/?LinkID=627338&clcid=0x409’ to ”.
WARNING: Unable to download the list of available providers. Check your internet connection.
Make sure to run in PowerShell: [Net.ServicePointManager]::SecurityProtocol = “tls12”
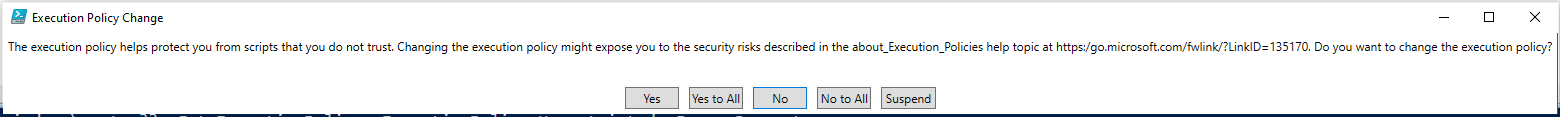
Make sure that your current user execution policy is set Unrestricted – Yes to All
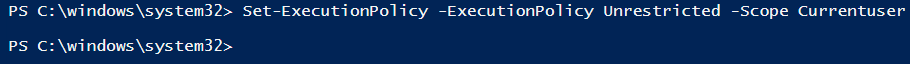
Set-ExecutionPolicy -ExecutionPolicy Unrestricted -Scope Currentuser
Change the path to the folder where you unzipped the module folder and run the .\CopyToPSPath.ps1 command.
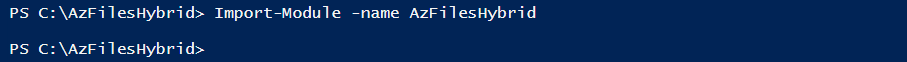
Import the Azure Files Hybrid Module
Import-Module -name AzFilesHybrid
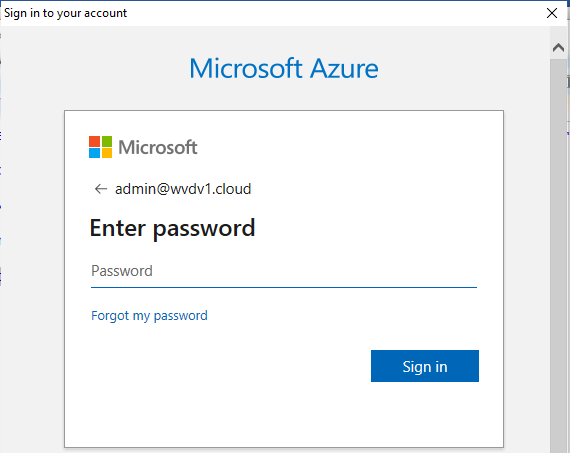
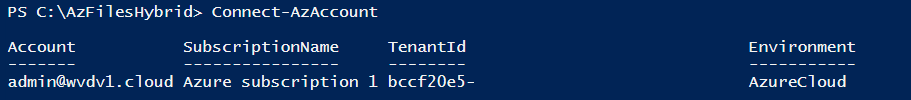
Connect to your Azure Subscription via PowerShell via command.
Note: This account needs to have at least owner rights on the storage account or contributor RBAC rights assigned with similar rights to perform the next tasks.
Connect-AzAccount
Now we need to select the subscription (name) for this current session
Select-AzSubscription -SubscriptionName "Azure Subscription Name"
Now the most important step starts. We are joining our Azure Files – storage account to our Active Directory (AD) environment.
Note: We need to run these commands from a computer/server that is part – joined to the Active Directory (AD) domain. It takes over the rights from the user that is logged which is running the PowerShell session so the user needs to have the domain administrator / delegated rights for that in place. It does not have to be a domain controller, but the command is using the ActiveDirectory PoSH module, so running it from a domain controller could be easier.
Note: The OU (friendly) name (not DN) is where the computer account to provide the LDAP connect is stored in. Make sure that the permissions on the OU level are correct. You can leave this empty – the computer account will then be created in the Root directly under your domain (not the computers OU).
join-AzStorageaccountForAuth -ResourceGroupName "<resource-group-name>" -Name "<storage-account-name>" -DomainAccountType "ComputerAccount" -OrganizationalUnitName "<OU--FRIENDLY-NAME>"
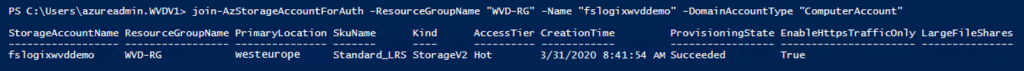
When the string ran successfully – you will see the following computer account – named as your Azure storage account – created in your Active Directory (AD) environment.
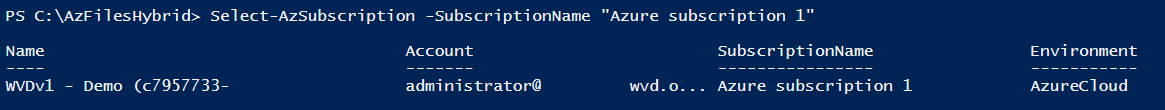
Verify if Active Directory is enabled
Go back to the Azure Portal and open the – Configuration menu – of your storage account.
Verify if Active Directory is enabled with your local domain name. See the below example.
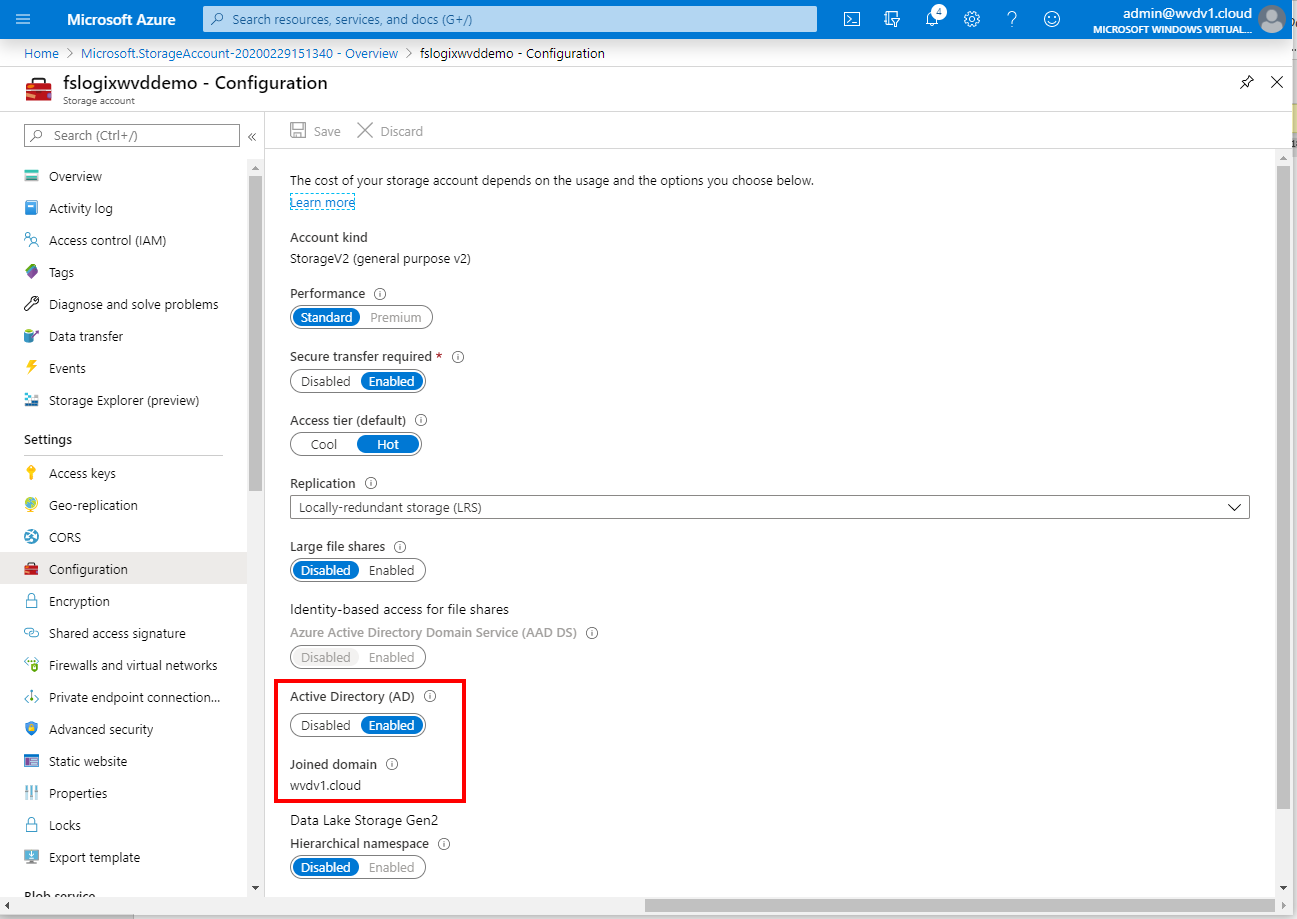
Configure IAM Object permissions – via the Azure Portal
Now we need to assign one of the built-in rights models to the specific file share to give users access to the Azure Files SMB share. There are three specific roles already available that we can use.
After we did these IAM steps – we can take over SMB share authentication on the NTFS level (with the elevated Contributor role) to make the folder rights more security and organization-specific.
- Storage File Data SMB Share Contributor
- Storage File Data SMB Share Elevated Contributor (NTFS configurations)
You can assign the user or AD group object rights via the IAM configuration menu of your storage account in the Azure Portal.
Note: If you use Groups – make sure the AD Group synchronized from local AD via Azure AD Connect. Azure AD Group only doesn’t work!
Note: Make one of your (data) administrators part of the Storage File Data SMB Share Elevated Contributor assignment. That gives you the extra privilege to configure (initially) the NTFS rights on the share.
Configure IAM Object permissions – via PowerShell
For sake of Automation with PowerShell we first have to create a couple of variables. The first one is to define the IAM role under $FileShareContributorRole.
$FileShareContributorRole = Get-AzRoleDefinition "Storage File Data SMB Share Contributor"
In the $scope variable we collect the File Service resource ID of the Azure Files Share location. You can find the path at the properties menu of your storage account. You only need to add the specific file share root folder manually after default (e.g. /fileshares/fslogixprofiles). See the example below.
Note: Make one of your (data) administrators part of the Storage File Data SMB Share Elevated Contributor assignment. That gives you the extra privilege to configure (initially) the NTFS rights on the share.
$scope = "/subscriptions/<AzureSubscriptionID>/resourceGroups/AVD-RG/providers/Microsoft.Storage/storage accounts/fslogixwvdfr/fileServices/default/fileshares/fslogixprofiles" $scope1 = "/subscriptions/<AzureSubscriptionID>/resourceGroups/AVD-RG/providers/Microsoft.Storage/storage accounts/fslogixwvdfr/fileServices/default/fileshares/msixappattach"
Perform the following command to Assign the specific IAM roles to the user.
New-AzRoleAssignment -SignInName username@domain.com -RoleDefinitionName $FileShareContributorRole.Name -Scope $scope New-AzRoleAssignment -SignInName username@domain.com -RoleDefinitionName $FileShareContributorRole.Name -Scope $scope1
To specify an AD security group for multiple users, use the Azure AD ObjectId parameter instead. First request the AD Group ID.
Get-AzADGroup -SearchString "AD Group Name"
Change the PowerShell command to the following example.
New-AzRoleAssignment -ObjectId 2f9d4375-cbf1-48e8-83c9-2a0be4cb33fb -RoleDefinitionName $FileShareContributorRole.Name -Scope $scope1
Verify access your Azure Files SMB Share
When we performed all the above steps correctly, we now can test if the share we created it accessible via our Azure Virtual Desktop environment and eventually configure FSLogix Profile Container.
Find the Azure Files Share UNC path at the storage account configuration menu.
Update 22.1.2021
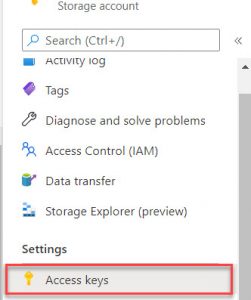
The IAM rights no longer reflect in the NTFS permissions, you must configure the NTFS permissions directly via the command below. Once you are connected to the share with the SA key, you can configure the rights based on your personal AD Domain Users and Groups. You can find the SA key under your storage account -> Settings -> Access keys.
net use <Drive letter> <Azure Files UNC-path> <SA-key> /user:Azure\<SA-name>
example code
net use Z: fslogixwvddemo.file.core.windows.net sjandksjadb2386236128612g /user:Azure\fslogixwvddemo
Continue the steps below
Logon as one of them (that you gave the rights to) user accounts – or a group member – to a domain-joined virtual machine. Try to access the Azure Files share, you have to add the folder to the location, such as \\fslogixwvddemo.file.core.windows.net\fslogixprofiles.
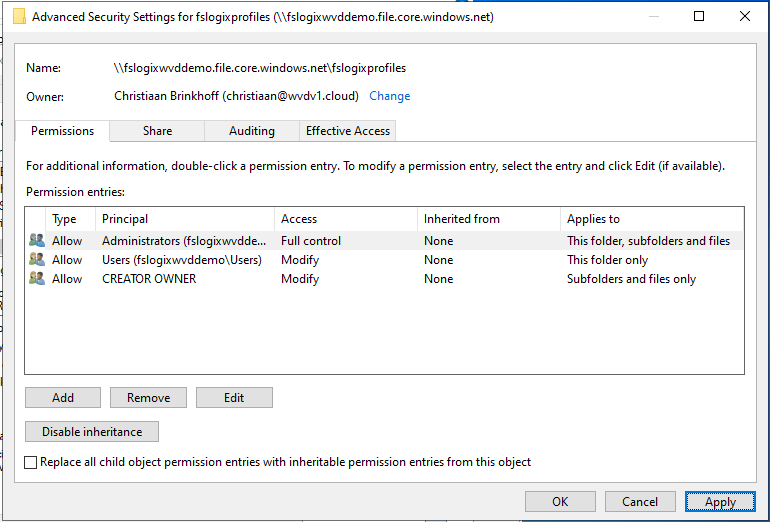
Configure NTFS rights on the Azure Files Share
You can start configuring all the NTFS rights that are recommended for the use of FSLogix Profile Container. See below the rights that are recommended to use for FSLogix. Read more about it here.
FSLogix Profile Container configuration
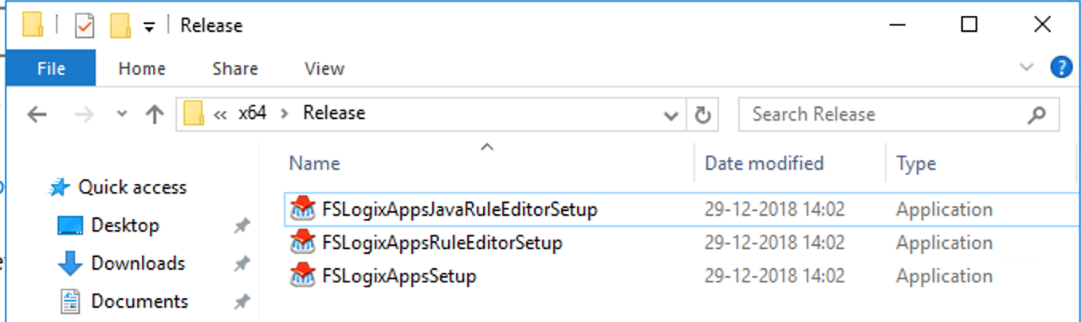
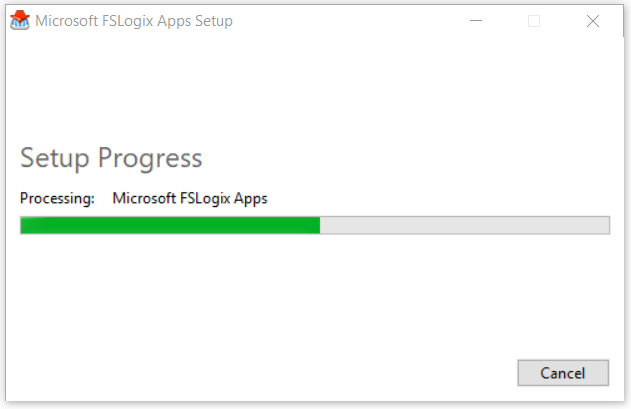
Download the FSLogix agent and install it in your Azure Virtual Desktop image – virtual machine. FSLogix is available for download here
Install the FSLogixAppsSetup agent in the image
Wait for the installation to be finished…
The configuration part of FSLogix Profile Container can be performed in either registry settings or group policy files. The most simple and effective method is using the registry settings below.
Open regedit.exe and browse to “HKEY_LOCAL_MACHINE\Software\FSLogix\Profiles”
Create a REG_SZ value name “VHDLocations” and enter new Azure Files network file share path (e.g. \\fslogixwvddemo.file.core.windows.net\fslogixprofiles)
Create a DWORD value name “Enabled” and give it value 1.
Create a DWORD value name “DeleteLocalProfileWhenVHDShouldApply” and give it value 1. The one deletes existing local profiles before logon – this avoids errors.
Create a DWORD value name “FlipFlopProfileDirectoryName” and give it value 1. The one changes the folder name to USERNAME-SID which is much easier during troubleshooting or maintenance search-related work.
Tip: The most important settings for the usage of FSLogix Profile Container are the Enabled and VHDLocations registry setting. There are some other settings that I default recommend to enable. The VolumeType setting changes to disk type to VHDX. You can provide more maintenance tasks via PowerShell with VHDx so I advise changing that from default VHD to VHDx.
Note: If you are using Windows 10 Enterprise single and multi-session or Windows Server 2019, you don’t have to enable the RoamSearch setting. The Search DB is already stored in your user profile.
See here all the other advanced registry settings for FSLogix Profile Container.
Scale Azure Files – storage accounts based on AD Groups
When you implement Azure Virtual Desktop on a larger scale – you could run into limitations of Azure Files. Premium storage accounts have up to max 100k IOPS per share with 5 GBps per share at about 3 ms latency. The rule of the thumb is that one user consumes between 5 and 15 IOPs (depending on the type of workload).
To work around this limit and stack up more Azure File shares to create more capacity – there is an option to create filters based on Active Directory groups. You must create an additional registry hive with the SID of that specific group after Software\FSLogix\Profiles and in that hive, you can create all the settings that must overrule the standard Profiles hive settings. This creates the option to filter/overrule settings for users that are members of the Active Directory Group – with effectively increasing on capacity – you can stack as much as storage accounts as you need to accommodate more IOPs.
HKLM\SOFTWARE\FSLogix\Profiles\ObjectSpecific\S-1-5-21-306146113-3061682913-806882557-2166\
Create in the registry hive a REG_SZ value name “VHDLocations” and enter the new (extra)Azure Files network file share path (e.g. \\fslogixwvddemo2.file.core.windows.net\fslogixprofiles). Repeat this for every group you create.
Read here more about the FSLogix ObjectSpecific settings.
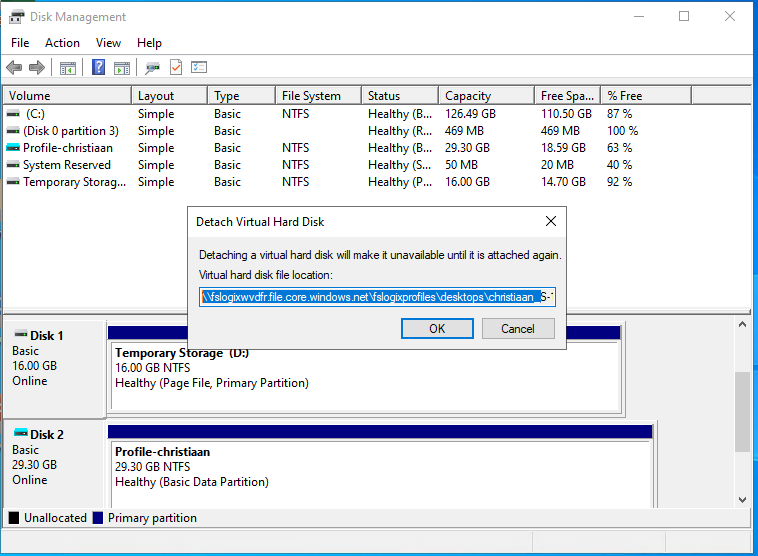
Verify FSLogix Profile Container on Azure Files
Logon as a specific user and check if the Profile Container is being created on the Azure Files share. See the example below.
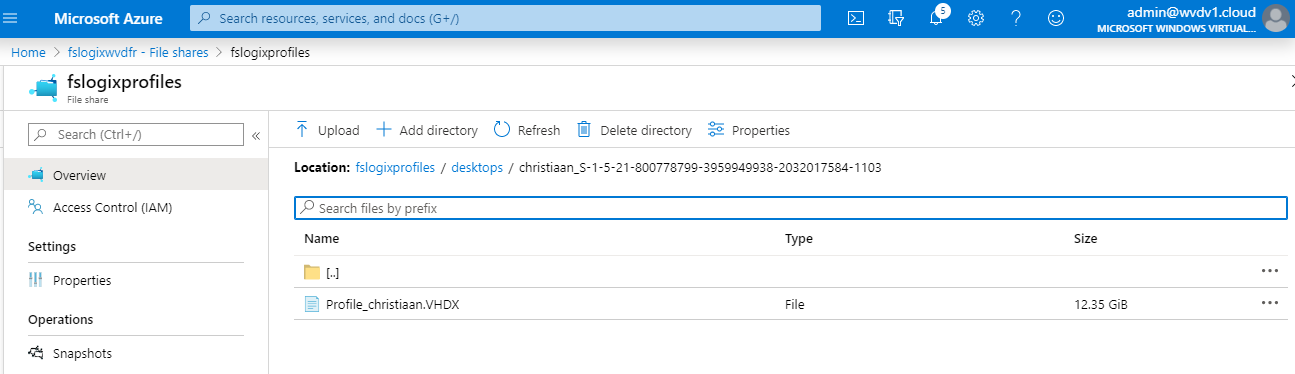
Or open the Disk Management (diskmgmt.msc) Console on your Azure Virtual Desktop – Windows 10 single – or multi-session virtual machine and see if it directly from there. All set!
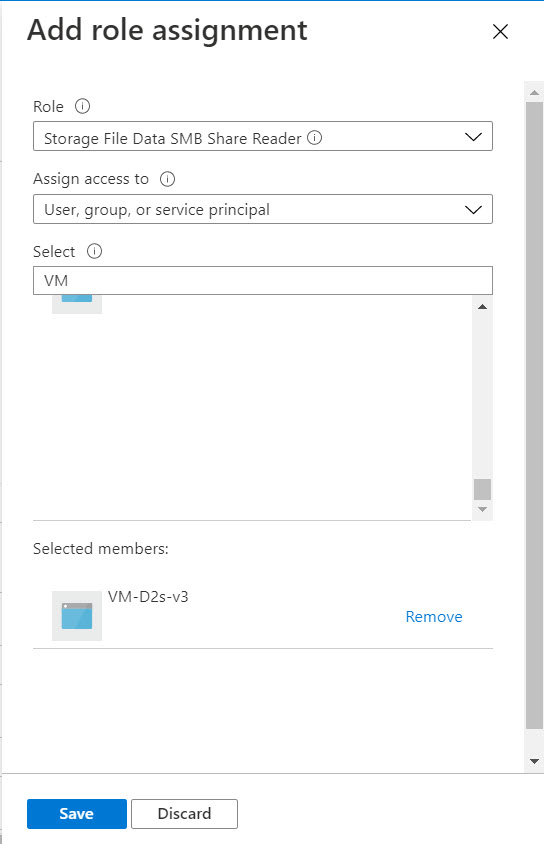
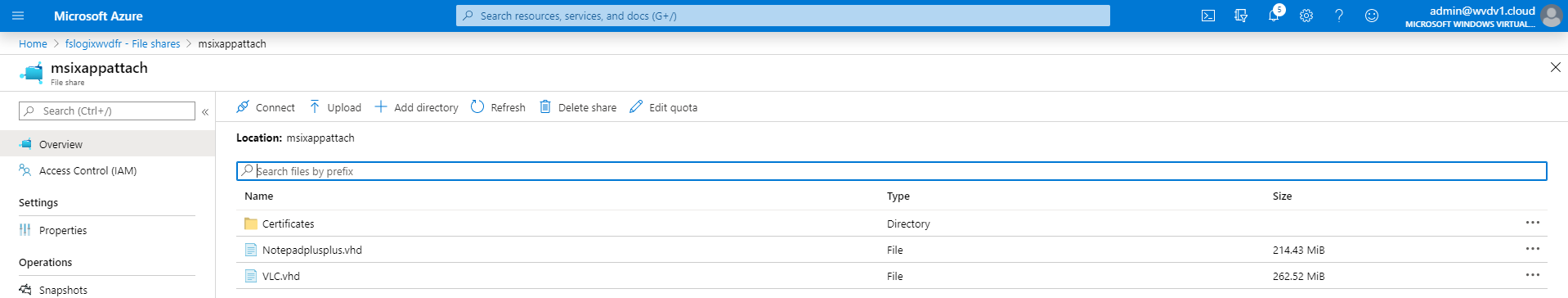
MSIX app attach NTFS and IAM rights configuration
MSIX app attach is currently in public preview. To configure MSIX app attach for Azure Files in the current public preview stage is fairly easy.
Make sure that all the MSIX app attach Container are stored in the designated Azure Files share location as for example below.
Copy / move the MSIX package on to the Azure FIles share
Before moving forward, make sure your session hosts can read to the Azure Files share! See below.
Make sure that the NTFS rights are set up correctly on the share, which means that the session hosts – computer account must be added to access (read-only) the Azure Files share where the VHDs are stored on! See also – Set NTFS ACLs for Azure Files here.
Note: Put all your session hosts, personal desktops in one Active Directory Group to make it easier and more dynamic to assign.
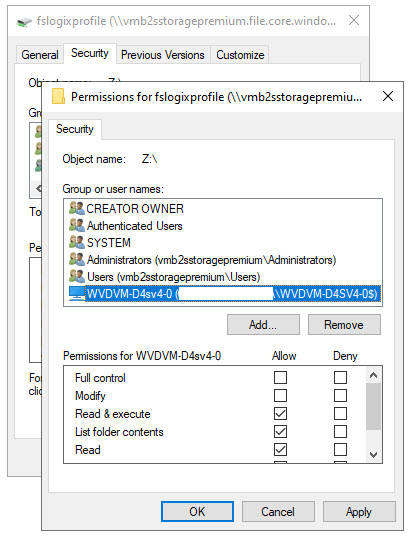
Also, make sure to add the computer account/AAD synced Group with (at least) read permissions on the Azure Files share as IAM/RBAC permissions to set the share level permissions correct with one of the two roles below – learn more here.
- Storage File Data SMB Share Reader
- Storage File Data SMB Share Contributor (optional)
Open the following page that whitelists the MSIX app attach application form within the URL.
https://preview.portal.azure.com/?feature.msixapplications=true#home
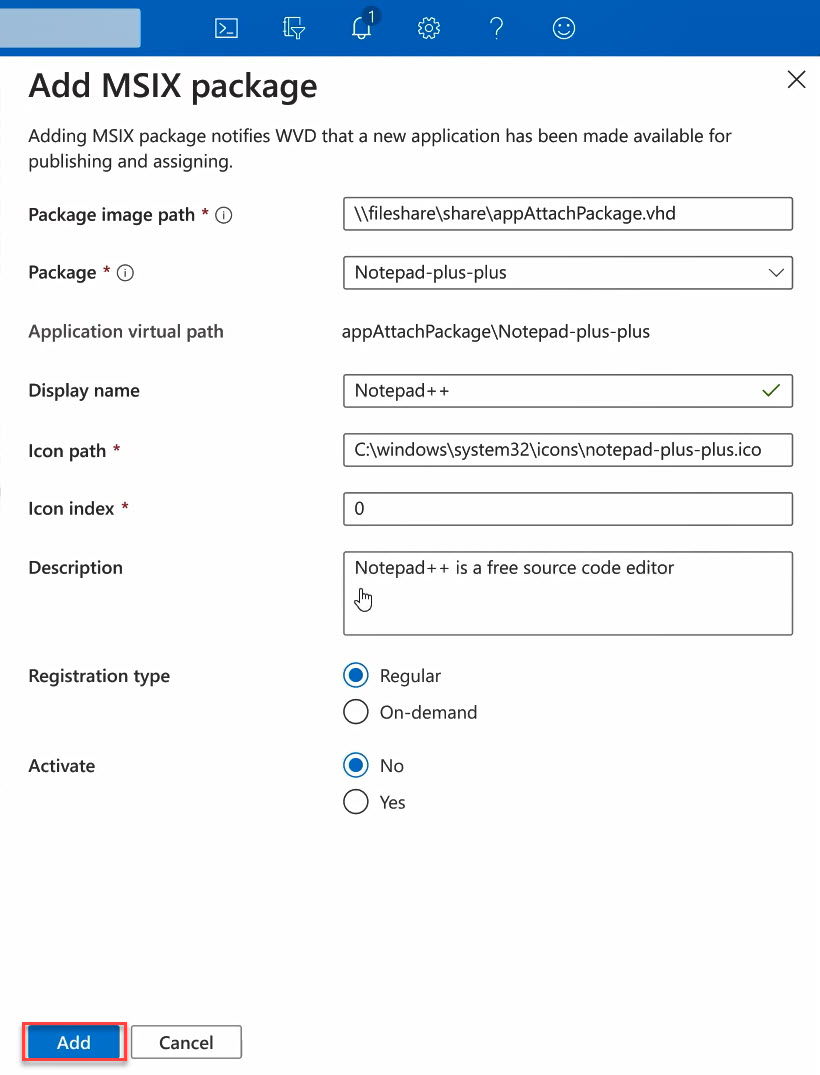
Add the Azure Files path + VHD(x) format into the field here.
Note: Make sure that the rights are set up correctly on the share, which means that the session hosts – computer account must be added to access (read-only) the Azure Files share where the VHDs are stored on!
Read more about how to use MSIX app attach here in one of my latest new blogs.
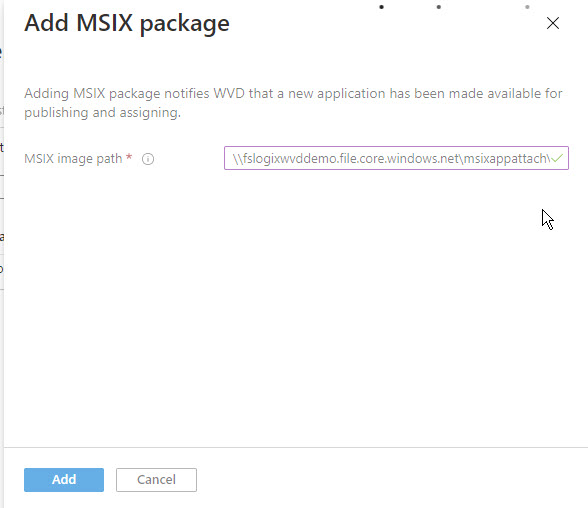
Assign the right VHDx – plus MSIX package, Display name, and Registration type settings. Make sure to put the application on Activate: Yes.
End-user– experience video
Learn more about the Azure Files and MSIX app attach at one of the latest presentations I did for the E2E Virtualization Conference. It includes information about the Azure Portal, concepts, and as well as Azure Files. A must watch in extension to this article.